Introduction
Rooted in African tradition of communicating and sharing spirit and knowledge in a circle, the cypher is a circle of MCs, B-boys/B-girls, beatboxers, djs etc who freestyle and/or battle one after the other without interruption, exchanging rhymes and flows back, forth, and around. The cypher (also spelled cipher) is where training takes place and skills are tested, where people collaborate, and where people create “off the top” or written/choreographed, tapping into the place where thought and action come together to share energy and advance the craft.
It is important to note that the concept of the cypher is rooted in Islam via The Nation of Gods and Earths (better known as The Five Percent Nation). Within The Five Percent Nation, the word cypher is used to refer to circle, zero, or the letter “0”. The phrase was used to describe a group of people situated in a circle having a discussion. There are several aspects of hip hop culture, specifically terminology, that is rooted in The Five Percent Nation, but has lost the connection or meaning over time.
Cyphers can be both spontaneous and planned. The key is that it is constantly moving in regards to both the participants and the content they create. The cypher is about creativity, individuality, community, competition, and equality. The performers–primarily, rappers or dancers—stand in a circle; each person takes a turn entering the center of the circle performing and then returning to the circle. Everyone in the cypher gets the chance to take part; participants are free to enter and leave the circle as they please. The audience, if there is one, is also a part of the cypher. They provide feedback via call-and-response, hype up the participants, and continue the content of the cypher by sharing the experience. Cyphers represent both the physical circle and participation in the cypher as well as the hip hop community at large. They are a space for training, battling, and community building: the cypher.
Literature Review: “Problem” with what a single (or any) theories have in analyzing your OoS.
Examinations of hip hop are nothing new to academia. In regards to English Studies, Hip Hop has been examined for its potential contributions to pedagogy, linguistics, and literacy. As a cultural practice, it has been studied for its history, role in the African diaspora, presentations of gender and sexuality, and socio-political impact. Most of these studies focused on the more popular aspects of hip hop—rapping, djing, and breakdancing–with little focus on the cypher. Most examinations Hip Hop in English Studies simply define the cypher as a point of reference within larger hip hop culture. There is little to no exploration or examination of it beyond it being a practice within hip hop culture. The limited amount of literature about cyphers focuses on two areas: language and pedagogy.
In “ ‘Bring it to the cypher’: Hip Hop Nation Language,” Alim presents that the cypher as a space where “the cultural modes of discourse are at their peak.” He examines the significance of language within the cypher stating, the cypher “is where all (or some combination) of Hip Hop cultural modes of discourse and discursive practices…converge into a fluid matrix of linguistic cultural activity. Works such as Newman’s “Rap Literacy: A genre analysis of Hip Hop ciphers” argue for the a multiliteracy approach to literacy by using the cipher as an example of “an oral vernacular genre” that challenges traditional conceptualizations of literacy.
Beyond its usefulness for language and literacy studies, the cypher has also been explored for its potential contributions to pedagogy. In “Framing and Reviewing Hip Hop Educational Research.” Petchauer argues that all aspects of hip hop are being utilized within academia to reach urban youth through critical pedagogy, to examine identity formation within the ethnic groups that utilize hip hop, and to explore historical and social aspects of hip hop. The focus on critical pedagogy can also be seen in the works of A. Dee Williams. In “The Critical Cultural Cypher: Remaking Paulo Freire’s Cultural Circles Using Hip Hop Culture,” Williams argues for the use of critical hip hop pedagogy to engage students in “a discourse of enlightenment” in order to develop “their use of counter-narratives,” “the language of critique and transcendence,” and “critical awareness (7).” The cypher was used as a foundation for the instruction, focusing on challenging, expanding, and constructing knowledge. There are many other works, which I do not have time to explore here, which examine hip hop pedagogy and cyphers for their usefulness in K-12 Urban Education. The key here is that the cypher is always literally translated in to the classroom by having students sit in a circle or by bringing hip hop texts/music into the classroom for students to discuss. Here the concept of a cypher and hip hop pedagogy is presented as a bridge between students day to day activities and ideologies and the curriculum.
Although there are only a few examinations of the cypher, these views situate the cypher as a significant part of hip hop culture with the potential to impact education. These works all provide definitions of the cypher and situate it as a significant tool of individual and collective expression. However, understanding the cypher as a network has the potential to move beyond examinations of cyphers as cultural artifact and beyond the cypher as a pedagogical tool through the literal classroom circle.
Cypher as Network
The cypher imagined as network would consist of the participants (performers, audience, and DJ), and the content of the performance as nodes in the network. In regards to agency, the cypher in its conceptualization is not hierarchical. The cypher is a circle; it has no beginning and no end, so there is no top or primary node. Agency within the cypher is supposed to be shifting yet equal. The agency shifts depending on who is performing at that time. The DJ, if there is a DJ, performs continually creating the background on which the performers create. Because cyphers can occur with or without some of the nodes, none of the nodes have more or less agency than the others. The nodes in a cypher should be interdependent, as one performer should be able to connect with and feed off of another performer. In a good cypher, the performers should be able to pick up the flow if another performer should make a mistake or lose the rhythm. This is also true in regards to the DJ. The performers should be able to connect with or vibe to whatever the DJ is playing in order to present their best material in the cypher. The most interesting part of the cypher is the content generated. Depending on the participants, the content of the cypher could be rappers, dancers, or DJs. If the participants are dancers, they are creating or presenting dance moves that others in the cypher will try to emulate or top. If the participants are DJs, they are creating music by presenting their variations or mixes of songs. Their content travels to the audience who can appreciate what is being played by dancing or show their lack of appreciation by not dancing.
If the participants are rappers, the content generated is speech/text. This content travels through the network via the audience, who can respond via call-and-response, cheering for the performer, or booing the performer. Within the cypher, the rappers content can also be interpreted by other rappers within the cypher. Another rapper may take parts from a previous rapper and transform them to benefit his/her particular message or flow. This can be done is a positive way as a form of admiration. It can also be done in a negative way as an insult or attack. The cypher as network emerges, most often, spontaneously. The cypher can also be planned. In that case, the network emerges or does not depending on how many people show up to participate. Just as the network appears spontaneously, it dissolves the same way. The cypher can stop or end at any point, depending on the energy of the participants and the content generated. The cypher may seem like a closed network in that it is localized. A particular group of people have to get to gether in a particular location for it to take place. This is a valid interpretation. However, the spontaneous nature of the cypher prevents it from being a closed network. The participants or nodes is every changing and the network can emerge or dissolve at any place at any time. The cypher network ebbs and flows.
Network Theories: What works from each theory? What part of their theoretical lens lets you look at something interesting?
There are two theories that can utilized to address the question “Why is studying my OoS useful to English Studies?” To do this, this study will utilize theories that focus on rhetorical activity. The hope is that these theories will illuminate the cypher as an overlooked aspect of hip hop culture, which deserves examination, and emphasize its usefulness to English Studies for teaching about rhetorical discourse and the research process. The theories utilized in this project are: Rhetorical Situation Theory, specifically Barbara Biesecker description of the rhetorical situation and Prior et. al’s remapping of the rhetorical canon via Cultural-Historical Activity Theory (CHAT). Ultimately, this paper will argue that using rhetorical situation theory and cultural historical activity theory as theoretical frameworks provide insight into cyphers as networked rhetorical activity. Moreover, these theories allow the cypher to be viewed as a metaphor for academic writing, particularly the research process (source use and knowledge construction).
Rhetorical Situation Theory: Barbara Biesecker challenged the conceptualizations of the rhetorical situation established by Lloyd Bitzer and Richard Vatz. Bitzer presented a hierarchy between the event and rhetor, which Vatz inverted. Biesecker challenges the binary of event and rhetor. Using, Derrida’s deconstruction and difference, she destabilizes the hierarchy. Biesecker points out the limitations of rhetorical discourse as focused on persuading and motivating action from expert/informed audiences. She argues that this conception of rhetorical situation ignores “discourses radically historical character” and “limits what we can say about discourse which seeks to persuade” (110). Moreover, rhetoric is said to have the power to modify or influence action, but cannot form new identities (111). Biesecker addresses these limitations by adding text and audience as a constituent elements of the rhetorical situation. Within the framework of differance, Biesecker’s addition of text presents that meaning is found in “the differencing zone,” which is contrary to Bitzer’s presentation of meaning being situated within the event and Vatz’s presentation of meaning being situated with the rhetor. According to Biesecker: “Derridean deconstruction begins by considering thè way in which all texts are inhabited by an internally divided non-originary ‘origin’ called différance” (120). This move away from origin allows theorists to move beyond the binary between event and rhetor; it expands the rhetorical situation in that ““neither the text’s immediate rhetorical situation nor its author can be taken as simple origin or generative agent since both are underwritten by a séries of historically produced displacements” (121).In addition, Biesecker gives agency to the audience, which is something Vatz and Biesecker overlook. Biesecker presents the human element of the network (both rhetor and audience) as being in flux, stating:
“From within the thematic of différance we would see the rhetorical situation neither as an event that merely induces audiences to act one way or another nor as an incident that, in representing the interests of a particular collectivity, merely wrestles the probable within the realm of the actualizable. Rather, we would see the rhetorical situation as an event that makes possible the production of identities and social relations. That is to say, if rhetorical events are analysed from within the thematic of différance, it becomes possible to read discursive practices neither as rhetorics directed to preconstituted and known audiences nor as rhetorics “in search of” objectively identifiable but yet undiscovered audiences.” (126)
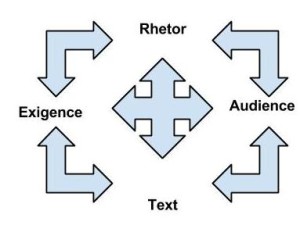
This approach to the rhetorical situation de-centers the subject This means that subjectivity is constantly evolving, nothing is a fixed point. Therefore, the constituents–exigence, rhetor, audience, and text—are nodes in a network that produces rhetorically situated discourse; however, there is no origin point or primary node. The rhetorical situation then produces and reproduces identities and the linkages between them. The subjects (rhetor and audience) and are moving parts of the network
The Cypher: Biesecker helps explain inner workings of the cypher as dynamic and interactive. The participants in a cypher (the performers and the audience) are all equal within the cypher. There is no primary node or origin point; each performer communicates with and feeds off the other performers and the audience, if there is one. Since they are not situated in a linear pattern, all the participants have the ability to generate content within the cypher at any time. However, the audience also impacts and generates content through call-and-response and other forms of yelling out, such as cheering and booing. They also impact content generation through their presence. For example, a performer within the cypher could mention the clothing or features of an audience member within his/her rap. Therefore, the relations among the performers, audience, and content is shifting; the rhetor, audience, situation, and content all impact and leave traces on one another. Meanings relay to other meanings which have been impacted by earlier meanings and then modified by later meanings. This process continues because language continues. Therefore, the content that travels through the network is continually impacted. It has the ability to fold back on itself, depending on the creative connectivity of the cypher. Because there isn’t a primary node and agency is shifting, meaning is found in the process of the rhetorical network; the content of the rhetorical situation is “on a trajectory of becoming rather than Being” (127). Therefore, the cypher emerges and grows, interacting and shifting. Biesecker’s description of the rhetorical situation, emphasizes the interactive and interminable nature of cypher. The cypher itself, on the local level, may end or dissolve; however, as the cypher is also a conceptualization of the members of the hip hop community, wherever “authentic” hip hop is taking place is the potential for cypher. Thus, the cypher as network is always in the process of becoming or taking place.
CHAT: Whereas the rhetorical situation theory focuses on why and how rhetorically situated discourse occurs, CHAT focuses on human activity and interactivity. According to Prior et al in “What is CHAT.” CHAT “argues that activity is situated in concrete interactions that are simultaneously improvised locally and mediated by historically provided tools and practices.” The tools range from machines to semiotics to name a few. The mediated activity includes speech/writing, interacting with others, and learning. CHAT traces these interactions as human or literate activity. These activities impact the environment, are embodied by the social organization, are mediated “over time and space among people, objects, and environment,” and are distributed across “social and historical boundaries.” Prior et al use CHAT to remap rhetorical activity, presenting rhetorical activity as literate activity that takes place within functional systems within laminated chronotopes. Literate activity is: production, representation, distribution, reception, socialization, activity, and ecology. This remapping of rhetorical activity is a network in that “it points to a complex set of interlocking systems within which rhetors are formed, act, and navigate.”
The Cypher: CHAT could possibly define cyphers as a the embodiment of hip hop presented through a combination of production, representation, distribution, reception, socialization, and activity within the functional systems of people, practices, and communities. The communication within cyphers are produced by participants within a particular context or moment, which symbolically connects to other contexts and moments via the concept of the cypher. The content generated within the cypher is “entextualized in talk, text, and mind” by the participants through their performances in the cypher. The performers modify the distribution of the content through their performance. The performers decide what to say, how fast, how long to perform, and how to physically enact their performance. The “actual reading/viewing/hearing and response” to the activity takes place simultaneously with the performance. This entire experience and the history of hip hop is socialization in that it enculturates participants. As they participate in the cypher, “they are involved in apprenticeship, learning, and development.” Lastly, activity deals with “goal-oriented, motivated projects that lead people to cooperation, indifference, and conflict.” Cyphers serve as a training ground for performers and a space to share information and construct/create knowledge. The goal of the cypher is to disseminate and perpetuate hip hop culture. Within CHAT the nodes are literate activity. Literate activity is “action and cognition[…] distributed over time and space and among people, artifacts, and environments […]” (Prior et. al). Therefore, nodes within the cypher would be the participants within the cypher and the content created because within the cypher, the content created and communication can loop back, impact, and facilitate the cypher. Through CHAT agency would shift between the users of literate activity. As mentioned above, the participants are responsible for production, distribution, representation, reception, socialization, and activity. The relationship between nodes is interactive. It functions as an “interlocking system within which rhetors are formed, act, and navigate” (Prior et. al). The participants in the cypher and and navigate the cypher literally and figuratively through their performance. The individuals are also formed by the cypher, as they are impacted by the content generated by the other participates (DJ, audience, and other performers). CHAT emphasizes ecologies, which operate within literate activity and function systems; ecologies “point to the biotic and natural world, which enables and constrains all the previous functions and which may also be a domain of rhetorical action” (Prior et. al). In this context, Hip Hop could serve as an ecology. The participants enter the cypher, which is a hip hop artifact, generate content and utilize the space of the cypher. Cyphers function is a system in which participants come together to mediate activity. CHAT allows for the cypher to be historically situated by tracing the cultural practices from individual activity to embodied within society. It also situates the cypher as a significant tool in hip hop culture for transformation and mediation.
Where each theory has a gap or misses a critical part of the OoS? Why these theories can be made to work well with each other? Rationale for bring your chosen theories together in order to create a new theory of networks that works for your OoS.
The cypher is a dynamic interactive network between participants in hip hop culture. Each theory allowed for different perspective of the participants and the content of the network, respectively. Where rhetorical situation theory dealt with the why and how of rhetorical discourse, CHAT dealt with the specific activity and how it functions beyond individuals (outside of the monologue between rhetor and audience). These theories provide a focus on rhetorical activity. Rhetorical situation and CHAT both speak to how rhetoric is produced. The theories are grounded in rhetoric as a response to a problem or in order to cause action on part of the audience. Biesecker presents this via the difference zone and the construction of identities. CHAT speaks to this through reception and socialization. In addition, agency is shifting within both theories. Biesecker avoids the binary between rhetor and event. Prior et. al also try to avoid this binary presenting the issue of rhetoric being “a model grounding in a speaker and hearer, essentially in monologue.”
Through Biesecker, agency is given to all parts of the network. There is no point of origin or hierarchy. Rhetorical situation theory deals with origin or production of actions without falling into the binary of rhetor or event. The move away from rhetoric as response, allows for the cypher to be seen as a space where both the content and subjects are modify, impact, and transformed. If the origin of the cypher become an issue, one could fall into a chicken and egg argument. Is the cypher started in response to a specific social or cultural issue? Does the cypher start organically? Does the cypher start out of a desire for creative expression? Through Biesecker the distinction isn’t necessary. The answer to all of these is yes. However, with the caveat that each of these situations is impacted by external elements and spaces of difference. However, rhetorical situation restricts the examination because it focuses on specific nodes. Although the nodes are not in a specific order (because of Biesecker’s theorization of the rhetorical situation), the nodes are limited to the examining the basic elements author, audience, and text. Biesecker does present these as interactive and impact by one another. However, they are not presented as collaborative, meaning they interact and connect but do not necessarily play a part in the creation. Rhetorical situation primarily focuses on persuasive action. It is important that Biesecker does make a distinction in regards to its ability to constructing identities. This focus does not allow for the tracing of collaborations and the significance in these collaborations in socializing or enculturating rhetors and audiences.
CHAT provides a focus on activity and social context, which rhetorical situation allows only through Biesecker. However, CHAT also allows for a discussion of all the elements of the cypher, while rhetorical situation theory does not allow for such a specific examination. Whereas, rhetorical situation theory can allow for a discussion of meaning and audience, CHAT allows for a discussion of the activity within a larger context in regards to the literate activities role in functional systems, such as institutions and communities. However, CHAT is limited in regards to what it affords for exploring the location/relationships of nodes and the emergence/dissolution of the network. The remapping of rhetorical activity is presented as network within network within a network. This presentation of embedded networks does not necessarily place the laminated chronotopes (embodied, represented, embedded activity) at the top of the hierarchy. Different parts of the network can be located within different categories in the Remapping Rhetorical Activity: Take 2. CHAT provides a greater examination of how the cypher works within a larger social context. However, it cannot account for individual human activity. The activity within the cypher (the individual creative expression) will be connected to larger system. All activity “is situated in concrete interactions that are simultaneously improvised locally and mediated by historically-provided tools and practices, which range from machines, made-objects, semiotic means (e.g., languages, genres, iconographies), and institutions to structured environments, domesticated animals and plants, and, indeed, people themselves.” Moreover, in regards to individuals, “people are socialized (brought into alignment with others) as they appropriate cultural resources, but also individuated as their particular appropriations historically accumulate to form a particular individuals. Agency is difficult to address here as the people are important to the interactions; however, they individuals are also shaped and formed by “particular appropriations historically accumulate.”
Why is studying my OoS useful to English Studies?”
Scholars in English Studies have already examined cyphers in terms of turning the classroom into a cypher and examining black vernacular English in terms of multiliteracy and social literacy. It would be interesting for cultural studies scholars to examine the construction and/or presentation of cyphers in different cultures. It would be interesting to see an examination of cyphers as early social networks, interactive oral narratives, and creative dissemination of news and history. In the concept and performance of the cypher, Rhetoricians could study freestyle (memory), improvisation (delivery and style), the circle and its representations (arrangement), and the content of or act of the cypher to generate content (invention). The cypher can be seen as a space of rhetorical activity to teach students about the rhetorical situation in a more dynamic fashion (similar to Biesecker), as well as the significance of these networks culture and information systems within specific communities. Cyphers also provide a way to discuss rhetoric and the production and movement of information. This is important for English studies as we move toward a more networked classrooms and teach students whose lives are digitally mediated. They will need the ability to think critically about the production and movement of information.
As a rhetoric and composition instructor, I find cyphers are useful as an object of study in English Studies because of their potential to illuminate academic writing, particularly the research process. They reflect and contest accepted constructions within the academy, potentially expanding the concept of the Burkean Parlor. Kenneth Burke’s parlor metaphor was presented in The Philosophy of Literary Form: Studies in Symbolic Action. Here the parlor is used as a metaphor for the “unending conversation”:
“Imagine that you enter a parlor. You come late. When you arrive, others have long preceded you, and they are engaged in a heated discussion, a discussion too heated for them to pause and tell you exactly what it is about. In fact, the discussion had already begun long before any of them got there, so that no one present is qualified to retrace for you all the steps that had gone before. You listen for a while, until you decide that you have caught the tenor of the argument; then you put in your oar. Someone answers; you answer him; another comes to your defense; another aligns himself against you, to either the embarrassment or gratification of your opponent, depending upon the quality of your ally’s assistance. However, the discussion is interminable. The hour grows late, you must depart. And you do depart, with the discussion still vigorously in progress.”
This metaphor is often used to introduce students, particularly freshman composition students, to the concept of academic writing being an “unending conversation.” Students are encourage to imagine themselves as entering this conversation. They are to listen for a while until they have the gist of the argument (research) and then join in the conversation (craft their position). From this students are to grasp the idea that writing is collaborative and a part of a larger conversation that has preceded them and will continue after they are gone. The focus here is on the interminable nature of conversation.
Through the conceptualization of the cypher as a network emphasis can be placed on aiding students in understanding and responding to sources. More importantly, the cypher can emphasize to the student the idea of becoming a source. The dynamic interactive nature of the cypher (similar to a conversation), emphasizes understanding the content of the cypher, as established by other participants, and then adding his/her ideas during the performance. The cypher places the same amount of weight on everyone’s contribution. This can provide a more inviting and accessible metaphor by which students can enter academic writing. Cyphers are a form of participatory culture, which can be utilized, akin to Henry Jenkins’ argument, to “reflect the new ways that young people are engaging with the world around them.”
Works Cited
Alim, H. Samy. “Bring it Into the Cypher: Hip Hop Nation Language” That’s the Joint! The Hip-Hop Studies Reader, 2nd ed. Murray Forman and Mark Anthony Neal, Eds. New York: Routledge, 2012. 30-563. Print
Biesecker, Barbara A. “Rethinking the Rhetorical Situation from with the Thematic of ‘Differance’.” Philosophy & Rhetoric 22.2 (1989): 110-130. Print.
Bitzer, Lloyd F. “The Rhetorical Situation” Philosophy & Rhetoric. Special ed. Selections from Volume 1. 25.1 (1992): 1-14. Print.
Burke, Kenneth. The Philosophy of Literary Form: Studies in Symbolic Action 3rd ed. California: University of California Press, 1973. Web. 6 May 2014.
Jenkins, Henry. “Confronting the Challenges of Participatory Culture: Media Education for the 21st Century (Part One).” Confessions of an Aca-Fan: The Official Weblog of Henry Jenkins. 20 October 2006. Web. 7 May 2014.
Newman, Michael. “Rap as literacy: A genre analysis of Hip-Hop ciphers.” Text, 23.5 (2005): 399-436. Print.
Petchauer, Emery. “Framing and Reviewing Hip-Hop Educational Research” Review of Educational Research, 79.2 (2009) 946-978. Print.
Prior, Paul, et. al. “Re-situating and Re-mediating the Canons: A Cultural-Historical Remapping of Rhetorical Activity: A Collaborative Core Text. Kairos, 11.3 (Summer 2007). Web. 31 March 2014. Web.
Vatz, Richard E. “The Myth of the Rhetorical Situation.” Philosophy & Rhetoric. 6.3 (1973): 154-161. Print.
Williams, A.D. “The Critical Cultural Cypher: Remaking Paulo Freire’s Cultural Circles Using Hip Hop Culture.” International Journal of Critical Pedagogy, 2.1 (2009): 1-29. Print.